Introduction
As I wrap up a fulfilling year with the incredible team at Aqua Security, I am filled with gratitude for the experiences and knowledge we’ve shared. Collaborating on innovative container security solutions has been a privilege. As 2025 approaches, I’m excited to embark on new ventures in API security.
This blog series encapsulates my insights as a Technical Customer Success Manager over the past 12 months, offering a high-level walkthrough of successful Cloud Native Application Protection Platform (CNAPP) implementations. While some concepts may seem straightforward, they are often overlooked in today’s fast-paced environment.
A crucial aspect not covered here is threat modelling. In our shift-left cybersecurity approach, integrating threat modelling into the design phases of all pipelines is fundamental. Tools like IriusRisk facilitate this threat modelling process with automation in mind and are worth exploring further.
Although focused on greenfield deployments, this 12 blog series can be referenced out of sequence and should provide valuable guidance. And yes, I did enlist ChatGPT to structure and refine my meandering thoughts and repetitive images.
Table of Contents
-
Setting the Foundations: Understanding Teams and Roles
- Current Article
-
Starting Small: Picking Pilot Teams for Initial Implementation
-
Scanning the Horizon: Shifting Security Left in the Software Supply Chain
-
Building Global Compliance: Establishing Assurance Policies
-
Dashboard Insights: The Value of Centralised Visibility
-
Real-Time Protection: Monitoring Active Workloads
-
From Pilot to Scale: Expanding CNAPP Across Teams
-
Securing the CI/CD Pipeline: Integration Best Practices
-
Reducing Noise: Optimising Alerts and Incident Reporting
-
Benchmarking Success: Adopting Standards and Frameworks
-
Empowering Developers: Tools for Secure Coding
-
Continuous Improvement: Sustaining a Secure Pipeline
Setting the Foundations: Understanding Teams and Roles
Securing a cloud-native pipeline is a team effort, and like any team, success hinges on clarity—clarity of roles, responsibilities, and access. Misaligned responsibilities or unclear accountability can result in vulnerabilities slipping through the cracks. For organisations navigating the requirements of NIS 2 and DORA, this alignment isn’t just best practice—it’s mandatory.
Roles such as Incident Response Teams, Application Security (AppSec), and Governance and Compliance Teams each bring unique skills to the table. Together, they form the backbone of a secure delivery pipeline, ensuring that vulnerabilities are tracked, mitigated, and reported in line with regulatory obligations.
Building the Foundation
Begin by identifying the stakeholders who will engage with your CNAPP implementation. These teams include:
-
Incident Response Teams: They react to threats in real time, leveraging forensic data to mitigate risks as they arise.
-
AppSec Teams: These specialists work within the SDLC, ensuring that vulnerabilities and misconfigurations are addressed before deployment.
-
Governance and Compliance Teams: Responsible for defining policies, maintaining compliance, and generating the reports mandated by NIS 2 and DORA.
-
CISO and Leadership: These executives require aggregated insights to guide strategy and maintain oversight of the organisation’s security posture.
NIS 2, for example, highlights the importance of operational resilience and accountability across teams, reinforcing the need for defined responsibilities.
Implementing Roles and Permissions with Aqua Security’s CNAPP
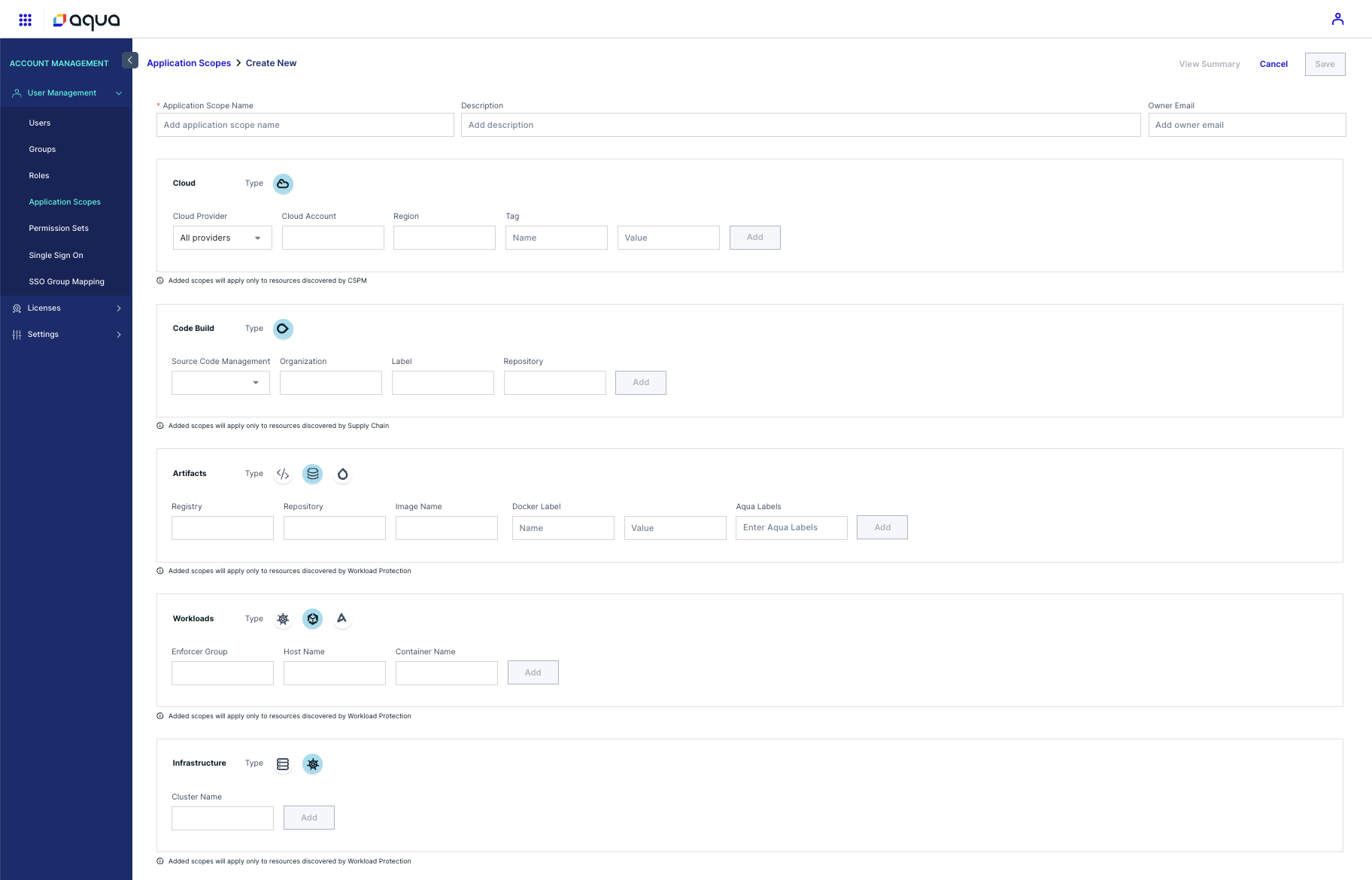
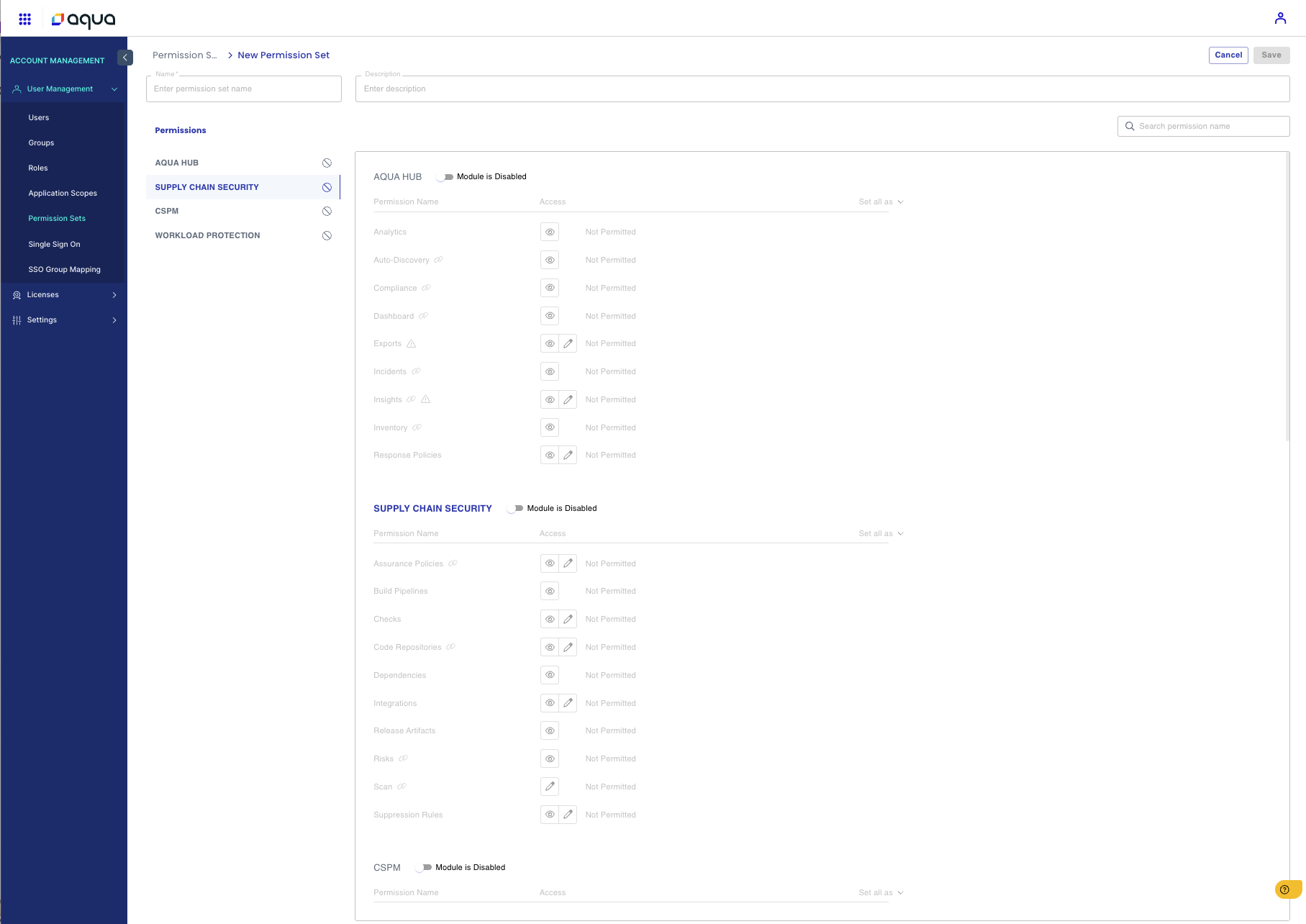
Using Aqua’s Role-Based Access Control (RBAC) features, organisations can assign precise permissions based on these roles:
- Start by mapping the necessary access levels for each team. For example, Incident Response may require access to real-time alerts, while Governance Teams may focus on compliance dashboards.
- Assign permissions at the team level, ensuring a clear segregation of duties.
- Educate stakeholders on their roles through onboarding sessions. Aqua’s user-friendly dashboards simplify this process, making it easier for non-technical teams to navigate their responsibilities.
As your organisation matures, these roles and permissions will need periodic review. Adjustments may include expanding access for AppSec teams to manage additional workloads or tightening controls for high-risk environments.
About Aqua Security and CNAPP
Aqua Security, founded in 2015, is a pioneer in securing containerised cloud-native applications from development to production. Their Cloud Native Application Protection Platform (CNAPP) integrates security from code to cloud, combining agent and agentless technologies into a single solution. (aquasec.com)
Aqua’s commitment to the open-source community is evident through projects like:
-
Trivy: A comprehensive vulnerability scanner for containers and other artifacts. (Trivy)
-
Tracee: A runtime security and forensics tool utilising eBPF technology. (Tracee)
-
CloudSploit: A tool designed to detect security risks in cloud infrastructure accounts. (CloudSploit)
These projects highlight Aqua’s dedication to enhancing container security and contributing to the broader cybersecurity landscape.
Summary
Clear roles are the cornerstone of a successful CNAPP implementation. By leveraging Aqua Security’s RBAC capabilities, teams can focus on their specific responsibilities without stepping on each other’s toes. This clarity not only enhances security but also ensures compliance with regulatory frameworks like NIS 2 and DORA. Begin with a solid foundation, and your pipeline will be better prepared to handle the challenges ahead.
Stay tuned for the upcoming blogs, where we’ll delve deeper into each aspect of securing your cloud-native applications.

Leave a comment